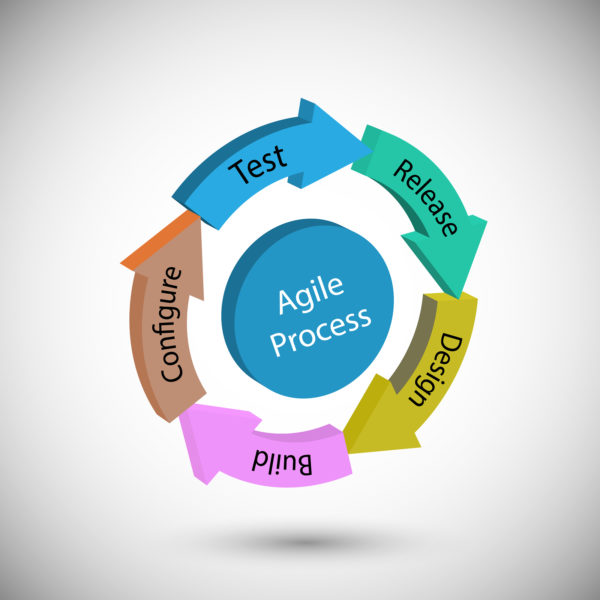
If you’ve been looking into the wonderful world of software development over the last few weeks and months, chances are you’ve come across agile test strategy examples… and chances are that you’ve been left scratching your head, puzzling over exactly what this entails and why it’s so important for you and your brand.
Why It’s Worth Investing In Software Testing
System Failure ‘Key Concern’ In Data Security
Why You Need Automation In Your Software Development Process
Australian Parliament In Hacking Attempt!
No matter the size of business or organisation you run, it’s essential that you prioritise the use of software test resources so you know you’re doing all you can to protect yourself against hacking and cyber crime.
Unfortunately, no one is safe these days and a good defence is most certainly you’re best offence when it comes to keeping your networks safe. Reuters has just reported on one of the most high profile cyber attacks to hit Australia, with its national parliament targeted by hackers earlier this month (February).
Although there is no evidence as yet that any data has been compromised or stolen, all those on site were instructed to reset the passwords on their computer networks as a precaution.
Director of the Centre for International Security Studies at the University of Sydney James Der Derian suggested that in order to carry out an attack of this nature, the perpetrators would need to have access to all sorts of big resources, so it’s most likely that a state-backed hacker is behind it.
Speaker of the lower House of Representatives Tony Smith and president of the upper house Senate Scott Ryan issued a joint statement on the matter, saying: “We have no evidence that this is an attempt to influence the outcome of parliamentary processes or to disrupt or influence electoral or political processes … Accurate attribution of a cyber incident takes time and investigations are being undertaken in conjunction with the relevant security agencies.”
If you’re worried about being targeted in a similar manner, it might be worth having a free health check carried out across the board so you know how well you’re performing and identify and control the inherent risks involved in your operations.